Research & Publications
Norcrest Technologies research explores deterministic, snapshot-bound control primitives for commit-gated activation of externally effective computing state, with independent verification by recomputation under immutable snapshot context.
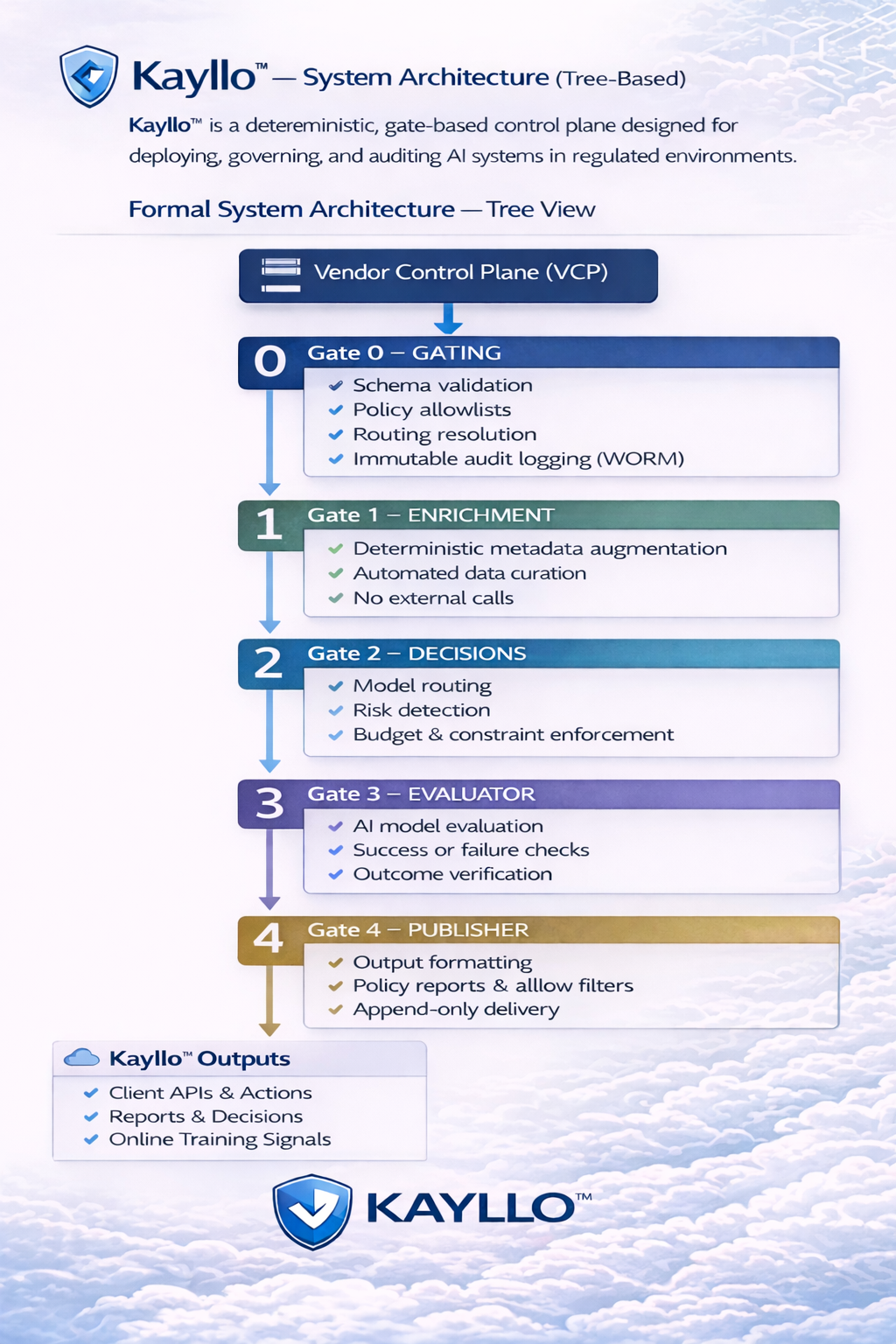
This research underpins Kayllo as the invention surface and Kayllo Control as the product implementation for AI agents, robots, drones, and autonomous systems.
External authority is not assumed from execution. It emerges only from a recorded deterministic state transition.
Commit-Gated Execution for Regulated Artificial Intelligence
Introduces commit-gated execution governance for regulated environments, separating provisional execution from externally effective outcomes.
Toward Commit-Gated Activation: Rethinking Authority Emergence in Autonomous Computing Systems
Proposes commit-gated activation as a control primitive governing when externally effective computing state can emerge under snapshot-bound verification.
Why this research matters
Many automated systems still couple generation to external effect. Norcrest research examines how to separate those layers so that computational output remains provisional until deterministic qualification and recorded transition make external effect possible.
Authority emergence
How and when externally effective computing state should be allowed to emerge in distributed and autonomous systems.
Verification by recomputation
How independent parties can validate authority-bearing outcomes through canonical artefacts and deterministic replay.
Append-only evidence
How evidence can be produced during transition rather than reconstructed afterward from mutable telemetry.
From research to product
This research is not isolated from deployment. It informs the architecture of Kayllo and the operational product delivery of Kayllo Control.
Kayllo
See the invention surface and control technology underlying deterministic qualification and commit-gated activation.
AI Agent Control
See how Norcrest’s control primitive is delivered in product form for AI agents and autonomous software systems.
What is AI Agent Control?
A practical definition page linking research concepts to production control requirements.
Research and collaboration opportunities
This work is intended for independent evaluation, critique, and experimental validation in distributed systems, verifiable computation, autonomous systems, control architectures, and infrastructure governance.
Collaboration is invited with academic and industrial research groups working in distributed systems, verifiable computation, autonomous and agentic systems, safety-critical automation, and infrastructure governance. Meaningful evaluation benefits from participation by independent institutions operating verification and experimental nodes under differing operational conditions.
Externally effective computing state models
Formal modelling of externally effective state within distributed systems theory and state transition semantics.
Verification by recomputation
Deterministic replay and verification methodologies independent of runtime environments and infrastructure vendors.
Verification networks
Interoperable verification networks operating across independently administered institutions and environments.
- Can externally effective computing state be formally defined within distributed systems models?
- What determinism guarantees remain achievable under heterogeneous infrastructure?
- How can independent verification nodes validate activation without trusted execution environments?
- What performance and safety trade-offs emerge when activation is separated from execution?
