Verification & Replay
High-trust systems require outcomes that can be independently verified. Norcrest defines a verification model based on canonical artefacts, append-only evidence, and export bundles that enable offline recomputation of transition identities under snapshot-bound context.
This verification model underpins Kayllo as the technology layer and Kayllo Control as the product delivery path for AI agent control, robot control, and drone control.
Traceability by construction
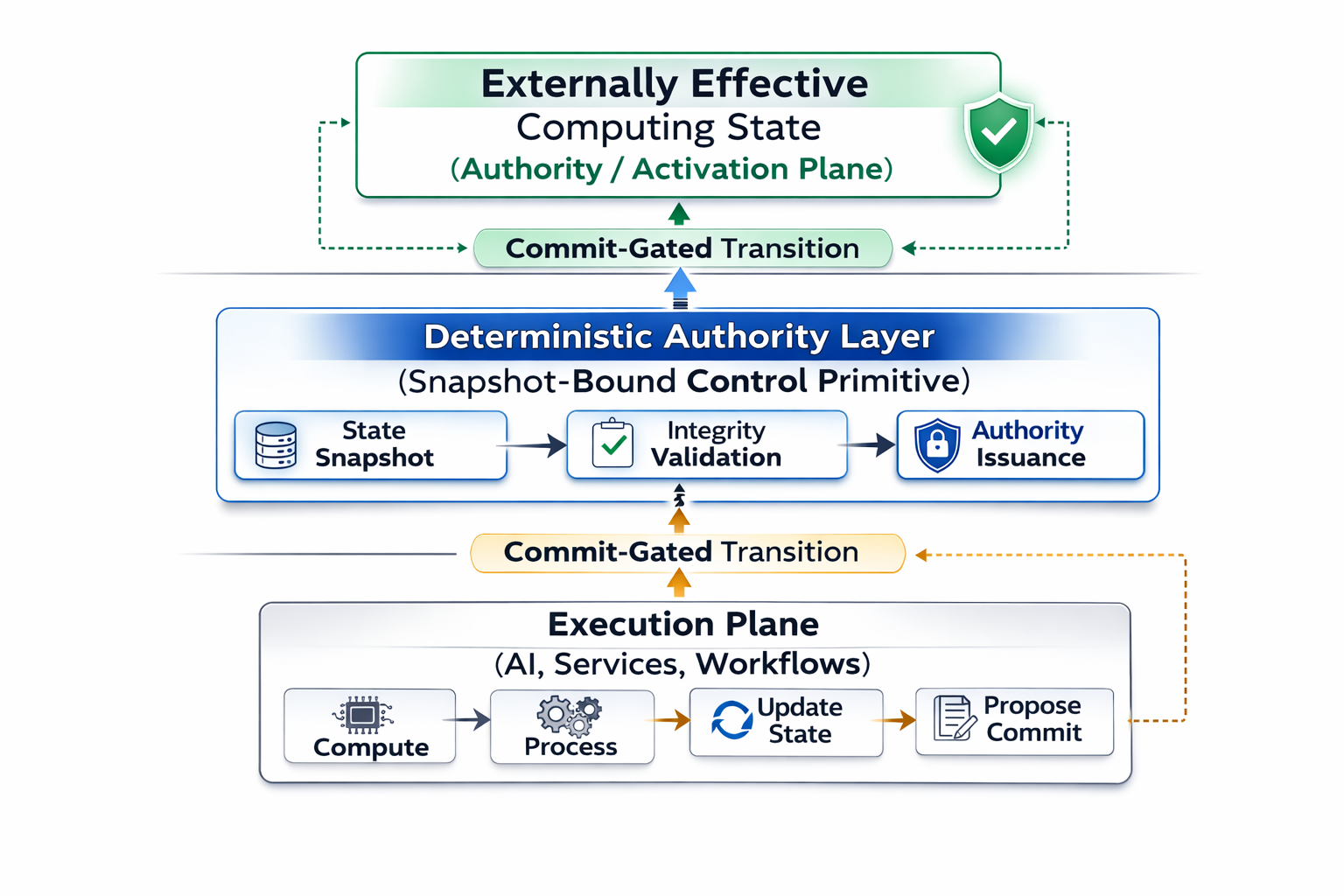
Externally effective outcomes bind to canonical transition evidence: snapshot identifiers, registry references, deterministic identities, and append-only commit records.
Independent recomputation
An external verification node can recompute transition identities using canonicalisation rules and exported artefacts under the same snapshot context.
Determinism breach detection
If recomputed transition identities differ under equivalent inputs and snapshot context, a determinism breach condition becomes observable.
What verification means in this model
Verification is not merely checking logs after execution. It is the ability to independently recompute the transition identity of an authority-bearing event using canonical artefacts and immutable snapshot context.
Conventional verification
- Depends on application logs and telemetry.
- Evidence may be reconstructed after the fact.
- Replay often breaks under runtime drift.
- Trust remains coupled to the original system.
Norcrest verification model
- Depends on canonical artefacts and snapshot-bound context.
- Evidence is preserved during transition flow.
- Replay supports deterministic recomputation.
- Verification can be performed independently.
Export bundle contents
Export bundles are immutable artefacts containing sufficient deterministic material to permit offline recomputation and verification.
- Canonical input envelope, or canonical envelope references
- Snapshot identifier and immutable registry version references
- Deterministic verification gate outputs and constraint results
- Deterministic transition identity and routing artefacts
- Execution result identity
- Canonical transition wrapper and transition identity
- Export hash over the canonical export bundle
Why verification matters for externally effective systems
Verification matters most when computational output can become externally effective — for example in AI agents, robotic systems, drone operations, and other autonomous environments.
AI Agent Control
Qualification and verification before agent proposals reach tools, workflows, records, or systems.
Robot Control
Deterministic verification before robotic commands become externally effective physical execution.
Drone Control
Evidence-backed verification before drone commands become externally effective flight operations.
From verification research to product delivery
Norcrest research defines the verification primitive. Kayllo expresses it as technology. Kayllo Control delivers it in product form for teams that need control and verification before execution.
